Someone Ran Doom Through DNS Because The Internet Is Unhinged

We all know the "can it run Doom?" meme at this point. Pregnancy tests, ATMs, tractors, oscilloscopes, a hundred potatoes wired together. If it has a processor and someone has too much free time, Doom is getting installed.
But this week, someone actually got me.
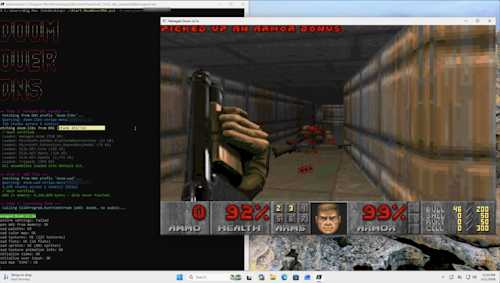
A security researcher named Adam Rice figured out how to store and execute the entire Doom game engine using nothing but DNS TXT records. Not a tech demo. Not a proof of concept. Actually playable Doom, loaded entirely through DNS queries, with nothing written to disk.
I had to read that twice.
How It Actually Works
DNS is boring infrastructure. It's the system that turns domain names into IP addresses. You type google.com, DNS tells your computer where to actually go. It's been running more or less the same way for 45 years. Nobody thinks about it.
But DNS also has these things called TXT records. They're just arbitrary text fields, originally meant for domain validation and spam control. No restrictions on what you put in them. No validation. Just raw text storage sitting on infrastructure that's cached across the entire internet.
Rice looked at that and thought: what if I put Doom in there?
Here's the process:
- Take the shareware version of Doom (about 4MB for the WAD file, 4.4MB for the DLL bundle)
- Compress everything down to roughly 3MB total
- Encode it as base64 text
- Split it across approximately 2,000 DNS TXT records on a single Cloudflare zone
- Write a 250-line PowerShell script that queries all those records, reassembles the data in memory, and launches the game
The loader is almost insultingly simple:
powershell
.\Start-DoomOverDNS.ps1 -PrimaryZone 'example.com'That's it. Run one command, wait 10-20 seconds for the DNS queries to resolve, and Doom loads directly into memory. No files on disk. No installer. Nothing your antivirus would ever flag.
The whole setup cost Rice $20/month for a Cloudflare Pro zone. He could've done it on the free tier with multiple domains, but apparently he felt bad about "abusing their free tier for cursed computing projects" too much.
The Security Implications Are Genuinely Terrifying
Here's the thing: Rice isn't just some hobbyist doing this for internet points. He's a security engineer, and the project started because he was thinking about how to hide malicious payloads in places nobody looks.
DNS TXT records are perfect for this.
Think about it. DNS traffic is almost universally permitted through firewalls because blocking it would break everything. Nothing gets written to disk, so file-based antivirus scans are completely useless. The payload is being delivered by the same infrastructure that resolves your grandma's cookie recipe website. And who's flagging the historic contents of TXT records? Nobody. That's who.
Rice has been using this technique in CTF challenges for a while, stashing malicious code in TXT records for implants to query at runtime. But Doom proves the concept scales way beyond simple shellcode. If you can store a payload, you can store a file. If you can store a file, you can store a program.
2,000 TXT queries in 20 seconds is technically an anomaly, but without dedicated DNS monitoring specifically looking for this pattern, it's going to slip right through. Most security teams aren't set up to catch it.
As Rice himself puts it: "It's trivially easy to set up and surprisingly annoying to catch forensically."
The Technical Rabbit Hole
For the nerds in the audience, here's some additional detail on how he pulled it off.
Rice needed a Doom port written in a language that could be loaded directly into memory without touching the filesystem. C# fits perfectly because .NET assemblies can be loaded from raw bytes via reflection. He found managed-doom, a pure C# port of the original engine, and modified it to handle stream-based WAD loading and run without audio (which took up too much space).
Each TXT record can hold up to about 2,000 characters, and a single domain can have thousands of records. After compression, everything fit comfortably in a single Cloudflare Pro zone at roughly 1,966 records.
The metadata records tell the loader how many chunks to fetch, hash values for corruption checking, and whether additional zones are needed. The loader script reads those first, then systematically queries each data record, reassembles the binary in memory, loads the assemblies via reflection, and launches the game.
No files written. No installation footprint. Just DNS queries and vibes.
Why This Matters Beyond The Meme
DNS was designed in the early 1980s to solve a simple problem: mapping human-readable names to IP addresses. The people writing RFC 1035 were not thinking about someone using it as a distributed file storage system decades later.
But infrastructure designed for one purpose always gets abused for others. That's just how the internet works.
Rice's project is funny. Running Doom through DNS is objectively hilarious and adds another entry to the "can it run Doom" hall of fame. But it's also a proof of concept for something security teams should probably start taking seriously.
If Doom fits in 2,000 TXT records, a lot of malware fits in way fewer. And the delivery mechanism is basically invisible to traditional security tools.
DNS tunneling isn't new. People have been encoding data in DNS requests for command-and-control communication and data exfiltration for years. But Rice's demonstration shows just how far the technique can scale with modern infrastructure and a bit of creativity.
At some point, security teams are going to need better DNS monitoring. Until then, the protocol that runs the internet is also a surprisingly effective covert channel for literally anything you want to hide in plain sight.
Including, apparently, a 30-year-old video game about shooting demons on Mars.
Source:
